AWS iam quiz
1/36: What is the correct way to add a policy allowing all IAM users in the group to have read-only access to Amazon S3 in the following IAM policy?
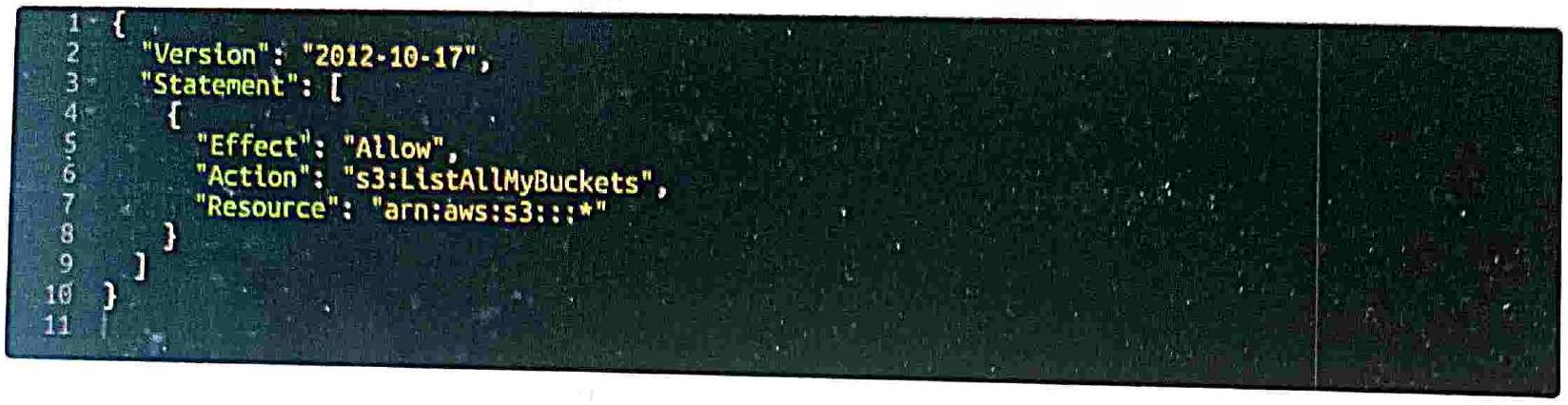
Replace the ˋs3:ListAllMyBucketsˋ action with ˋs3:GetObjectˋ.
Add a new statement with the ˋs3:GetObjectˋ action and ˋarn:aws:s3:::* resource.
- Add a new statement with the ˋs3:GetObjectˋ action and ˋarn:aws:s3:::bucket-name/*ˋ resource.
Replace the ˋs3:ListAllMyBucketsˋ action with ˋs3:GetBucketˋ.
List of questions
2/36: What is the correct way to add a policy that allows an IAM user to have read-only access to Amazon DynamoDB tables in the following IAM policy?
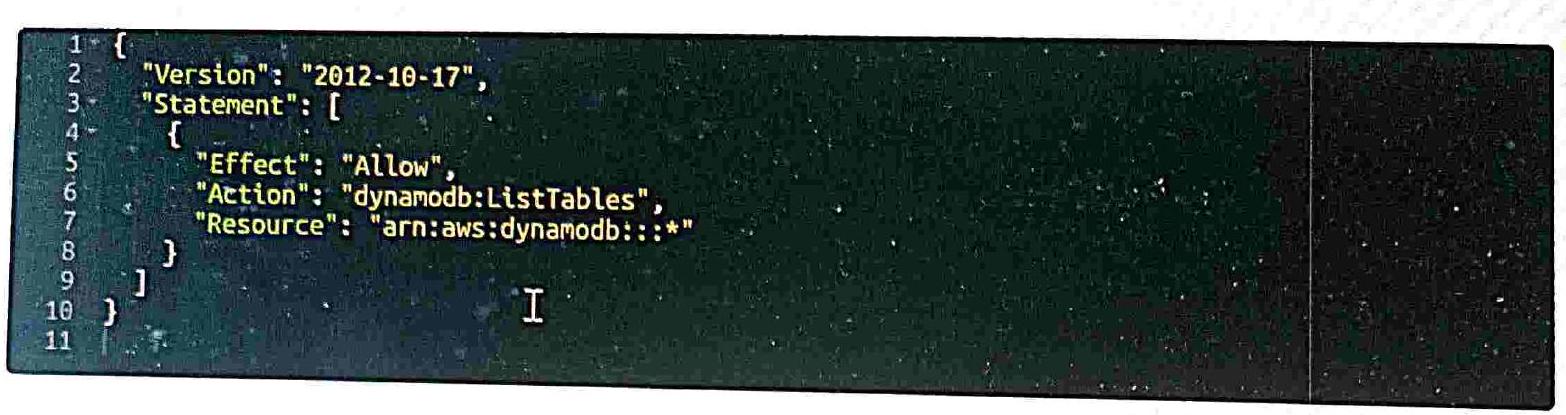
◯ ◯ Replace the ˋdynamodb:ListTablesˋ action with ˋdynamodb:DescribeTableˋ. ◯ ◯ Add a new statement with the ˋdynamodb:ReadItemˋ action and ˋarn:aws:dynamodb:::table/table-nameˋ resource.
- Add a new statement with the ˋdynamodb:GetItemˋ action and ˋarn:aws:dynamodb:::table/table-nameˋ resource. $____$ □
3/36: Which of the next AWS services have resource policies?
Section titled “3/36: Which of the next AWS services have resource policies?”KMS
S3
SNS
SQS
AWS Secrets Manager
- All of them
Previous
4/36: Review the IAM policy. Does it allow user to write files to a test-bucket? ◯
| 1-16 2 “Verston”:“2012-10-17”, 3- “Statement”:[ 4” { 5 “Effect”: “Allow”, 6 “Actton”: “s3:PutObject” 7 “Resource”: “test-bucket” 8 ] 9 ] 10 ] |
|---|
◯ li… ◯ Yes. The policy is correct. □ ◯ No. ˋarn:aws:s3::test-bucket/*ˋ resource should be used. ◯
No. Action should be replaced with ˋs3:PutObjectAclˋ. ◯
No. ˋtest-bucket/” resource should be used. ◯ No. “test-bucket/” resource should be used. ◯ Previous ◯ (コ) 1 ← List of questions
$____$
(1) 00:24:59 □
5/36: When would you use an Inline Policy over a Managed
Section titled “5/36: When would you use an Inline Policy over a Managed”Policy?

◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯
To add IAM permissions that can be applied to multiple AWS accounts that you own
When you want to change policies that are attached to multiple principal entities.
To add permissions that are only ever intended to be used for a single user in your account
To add IAM permissions for common use cases like giving your DBAs full access to DynamoDB
Previous
6/36: Which policies can be used with IAM Roles
Section titled “6/36: Which policies can be used with IAM Roles”- 7/36: What is the correct option for an IAM policy that allows a user to perform all S3 actions on all objects within a specific S3 bucket except for the “s3:DeleteObject” action? (Chose 2)
Include a Deny statement with an Action value of “s3:DeleteObject” and a Resource value of “arn:aws:s3:::mybucket/”“.
Include an Allow statement with an Action value of “s3:*” and a Resource value of “arn:aws:s3:::my-bucket”.
Include an Allow statement with an Action value of “s3:*” and a NotAction value of “s3:DeleteObject”.
Include a Deny statement with an Action value of “s3:DeleteObject” and a Resource value of “arn:aws:s3:::mybucket”.
8/36: Which of the following correctly describes an Inline Policy?
Section titled “8/36: Which of the following correctly describes an Inline Policy?”You cannot change the permissions defined in the policy □ The policy will be deleted if you delete the user, group or role it is associated with □ It is embedded in a user, group or role
It can be attached to multiple users and groups within your AWS account $)$ Previous
9/36: Which of the following applies to an AWS Managed Policy?
Section titled “9/36: Which of the following applies to an AWS Managed Policy?”It can only be assigned to a single user, group or role in your account
AWS occasionally updates the permissions defined in an AWS managed policy
It is available for use by any AWS account
You can change the default permissions defined in the policy ◯ ◯ ◯ ◯ ◯
10/36: How can you allow a user from one AWS account to access and manage resources in another AWS account?
Section titled “10/36: How can you allow a user from one AWS account to access and manage resources in another AWS account?”Configure web identity federation
Configure cross-account access
Configure Cognito
Configure cross-origin resource sharing
11/361 Which of the following API calls can be used to enable a user authenticated by Facebook to access your web application hosted in AWS?
Section titled “11/361 Which of the following API calls can be used to enable a user authenticated by Facebook to access your web application hosted in AWS?”
Assidins tolls dobettan talo withis adml
H/SVITHS
00:23:54
12/36: Which of the following types of security credentials can be assigned to an IAM User?
Access Keys
MFA Device
Console Password
SSH Key Pair for access to an EC2 instance X. 509 certificate for the Console login ◯ Previous ◯ ◯ ◯ ◯
13/36: What is the correct option for an IAM policy statement that allows a user to perform the “ec2:DescribeInstances” and “ec2:StartInstances” actions on all Amazon EC2 instances?
Section titled “13/36: What is the correct option for an IAM policy statement that allows a user to perform the “ec2:DescribeInstances” and “ec2:StartInstances” actions on all Amazon EC2 instances?”Action value is “ec2:” and resource value is ““.
Action values are “ec2:DescribeInstances” and “ec2:StartInstances” and resource value is “arn:aws:ec2::instance/*“. Action value is”ec2:” and resource value is “arn:aws:ec2::instance/”.
Action values are “ec2:Describelnstances” and “ec2:StartInstances” and resource value is “arn:aws:ec2::instance/”.
14/36: Pick security best-practices in AWS.
Section titled “14/36: Pick security best-practices in AWS.”Grant least privilege
Enable MFA
Use roles for delegating permissions
Store AWS credentials in safe on GIT
Use dedicated IAM Role for each AWS Region
15/36: Which of the following is NOT a feature of IAM?
Section titled “15/36: Which of the following is NOT a feature of IAM?”Identity federation for delegated access to the AWS Management Console or AWS APIs
Fine-grained access control to AWS resources
Centralized control of your AWS account ◯ Biometric authentication, so that no passwords are required
16/36: What entity can’t be a principal?
Section titled “16/36: What entity can’t be a principal?”Role
AWS services
User
17/36: Which IAM entity can you use to delegate access to trusted entities such as IAM users, applications, or AWS services such as EC2?
Section titled “17/36: Which IAM entity can you use to delegate access to trusted entities such as IAM users, applications, or AWS services such as EC2?”Web Identity Federation
Section titled “Web Identity Federation”Group
User
O) Role
Section titled “O) Role”18/36: A company wants to control access to its AWS resources by using identities and groups that are defined in its existing Microsoft Active Directory. What must the company create in its AWS account to map permissions for AWS services to Active Directory user attributes?
Groups
Users
Access keys
19/36: Using these parts of I/M polley you could make it applicable for wider range of users/resources
Section titled “19/36: Using these parts of I/M polley you could make it applicable for wider range of users/resources”- stct
Constition
Wildromis
Version
Arthon
Reserylle
Previour
20/36: Programmatic access to AWS requires
Section titled “20/36: Programmatic access to AWS requires”Secret user name
OTP Password
Access Secret ID
Secret access key
SSH Key
Access key ID
Previous
21/36: Which of the following correctly describes a Customer Managed Policy?
Section titled “21/36: Which of the following correctly describes a Customer Managed Policy?”It can be assigned to multiple users, groups or roles in your account
It is created and administered by AWS
The policy will be deleted if you delete the user, group or role it is associated with
It is managed by you
Previous
22/36: What is the limit of IAM Role policy size?
Section titled “22/36: What is the limit of IAM Role policy size?”4096 characters
Section titled “4096 characters”8192 characters
10240 characters
16384 characters
Previous
23/36: A developer designed an application on an Amazon EC2 instance. The application makes API requests to objects in an Amazon S3 bucket. Which combination of steps will ensure that the application makes the API requests in the MOST secure manner?(Choose 2) ◯ Create an IAM user that has permissions to the S3 bucket. Add the user to an IAM group. ◯ Create an IAM role that has permissions to the S3 bucket.
- Add the IAM role to an instance profile. Attach the instance profile to the EC2 instance.
Create an IAM role that has permissions to the S3 bucket. Assign the role to an IAM group.
Store the credentials of the IAM user in the environment variables on the EC2 instance.
Assign IAM group to EC2 instance.
24/36: Which of the following features of IAM allows you to have your users Authenticate using Facebook, Google or Amazon?
The IAM HTTPS API
Web Identity Federation
Multi-Factor Authentication
AWS Single Sign-On (SSO)
Previous
25/36: A Solutions Architect created a brand new IAM User without any policies attached. This is intended to be used to only send API requests to Amazon S3, DynamoDB, Lambda, and other AWS resources of the company’s cloud infrastructure. Which of the following must be done to allow the user to make API calls to the AWS resources using AWS CLI?
Create console management password for the user.
Enable Multi-Factor Authentication for the user.
- Create a set of Access Keys for the user.
- Assign an IAM Policy to the user to allow it to send API calls. ◯
◯ ◯ O

26/36: Which permission allows services to perform actions on your behalf?
Section titled “26/36: Which permission allows services to perform actions on your behalf?”sts:AssumeRole iam:PassRole iam:GetRole iam:RequestRole
Previous Finith
List of questions (1) 00:22:09
27/36: IAM role could be passed to EC2 instance with help of
Section titled “27/36: IAM role could be passed to EC2 instance with help of”Instance permission
Section titled “Instance permission”)
Instance policy
Instance profile
IAM Group
Section titled “IAM Group”28/36: Which of the following can you use to test that an IAM policy attached to a user, group or role works as expected?
Trusted Advisor
Lambda
IAM Policy Simulator
IAM Access Analyzer
29/36: Which of the following are provided by AWS to allow you to easily assign IAM permissions to your users based on predefined common use cases?
Common Policy
Managed Policy
Inline Policy
Custom Policy
Previous
00:21:46
J 30/36: Which format does IAM policy have?
Section titled “J 30/36: Which format does IAM policy have?”TXT
YAML
JSON
XML
Previous
31/36: Which is the best way to enable S3 read-access for an EC2 instance?
Create an IAM role with read-access to S3 and assign the role to the EC2 instance
Configure a bucket policy which grants read-access based on the EC2 instance name
Create a new IAM role and grant read-access to S3. Store the role’s credentials locally on the EC2 instance and configure your application to supply the credentials with each API request
Create a new IAM group and grant read access to S3. Store the group’s credentials locally on the EC2 instance and configure your application to supply the credentials with each API request.
32/36: What is an IAM Policy?
Section titled “32/36: What is an IAM Policy?”A CSV file which contains a users Access Key and Secret Access Key
The policy which determines how your AWS bill will be paid
A file containing a user’s private SSH key (-) AJON document which defines one or more permissions
Previous
33/36: Which statement best describes IAM?
Section titled “33/36: Which statement best describes IAM?”

◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯
IAM allows you to manage users’ passwords only. AWS staff must create new users for your organization. This is done by raising a ticket.
IAM allows you to manage permissions for AWS resources only.
- IAM allows you to manage users, groups, and roles and their corresponding level of access from AWS.
IAM stands for Improvised Application Management, and it allows you to deploy and manage applications in the AWS Cloud.
Previous ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯
34/36: This AWS service allows you to create temporary credentials for AWS CLI/API/Console:
Section titled “34/36: This AWS service allows you to create temporary credentials for AWS CLI/API/Console:”AWS SSM
AWS SNS
AWS SMS
- AWS STS
Previous
и… ஒ 35/36: IAM roles are …
Section titled “и… ஒ 35/36: IAM roles are …”◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯ ◯
AZ resource
Regional
Section titled “Regional”- Global
Previous Filish
36/36: An IAM user requires access to the AWS Management Console and must use multi-factor authentication (MFA) every time they sign in. What is the minimum set of permissions required to enforce this requirement in an IAM policy?
The ˋiam:CreateLoginProfileˋ action and ˋiam:AddUserToGroupˋ action.
The ˋiam:CreateMFADeviceˋ action and ˋiam:PassRoleˋ action.
The ˋiam:RequireMFADeviceˋ action and ˋiam:PutUserPolicyˋ action.
- The ˋiam:CreateLoginProfileˋ action and ˋiam:CreateVirtualMFADeviceˋ action.